Category: Tech and Coding
-
How to Solve Email
Universal problem, circa 2000: you move around from school to school, job to job, Internet provider to Internet provider. They all give you email addresses, which of course constantly change. What a headache.

-
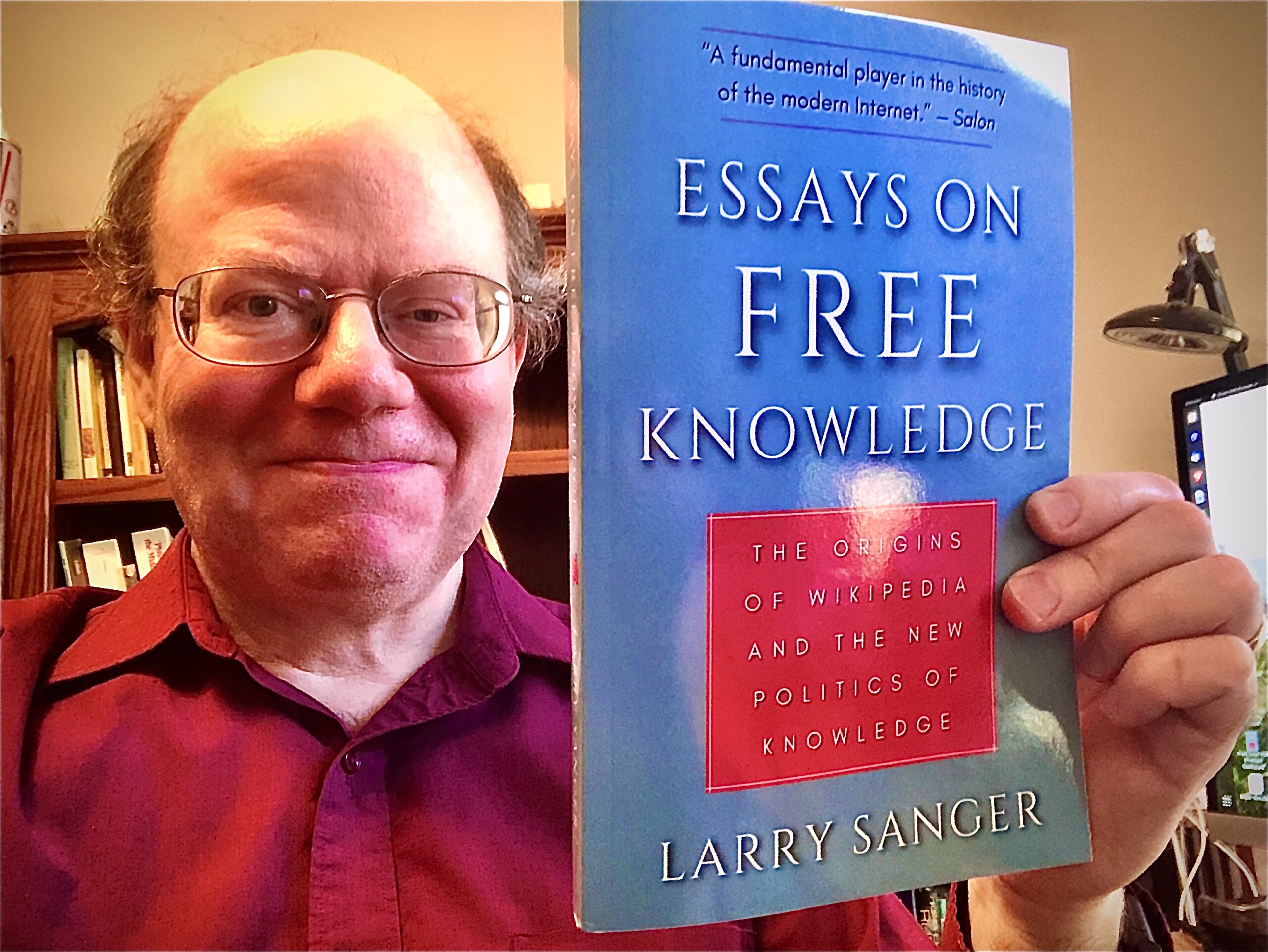
What Next?
I am an odd fish, I admit. Let me explain, as much to myself as to you, my life path and where it seems to be leading next. My Strange Career I wanted

-
Launching Sanger Consulting
I’m announcing an Internet consulting business. Learn more at a new website: > sanger.io < I’ve consulted briefly with many companies over the years. Nobody seems disappointed. The thing that I can do
-
The challenges of locking down my cyber-life
In January 2019, I wrote a post (which see for further links) I have shared often since about how I intended to “lock down my cyber-life.” That was six months ago. I made

-
How to write an app (that respects privacy and supports security)
Some difficult-to-meet requirements Be open source. Don’t make users have to trust your black box. I don’t want to have to trust you. I don’t know you. Don’t just release your in-house source
-
Why your company should consider getting a NAS
What’s a NAS again? “NAS” means “network-attached storage,” but this buzzphrase has come to mean more than just a backup drive for your local network. It’s also, and maybe more importantly, an easy-to-set-up